For many years I have always changed my SSH ports to a non-standard port number. Typically the default port number for SSH is 22. I think it's a good idea, but port scanners can easily go through all your ports to figure out what port SSH might be listening on, especially if it identifies itself as SSH. For example, if you were to correctly guess the port number that our server uses for SSH you would see something like this:
With that said on our server we also have an SPI Firewall, or in other words, a firewall that does stateful packet inspection. That is a system that will track connections, analyze incoming packets, etc. One thing that ours does is to monitor failed attempts with users connecting to ports, and if someone attempts a port scanning attack to try and obtain more information, our server will immediately ban the offending IP address. This doesn't entirely prevent someone from discovering what port SSH may be running on, but it will make it more difficult.
You could also enable port knocking. With that, a user would have to guess the correct sequence of ports to connect to before it would be allowed to create a session. That would be extremely difficult.
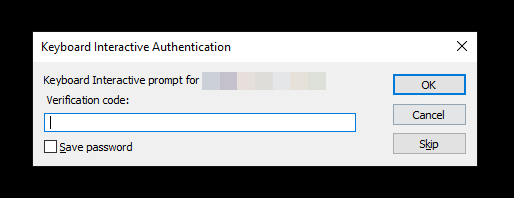
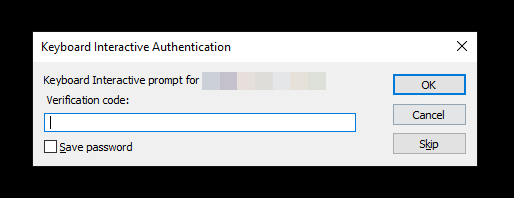
Another way which I recommend is to enable two-factor authentication with SSH which can help ensure that if someone found your SSH port, and somehow knew your username and password (perhaps from a password sniffer for instance), they would still need the random code that is usually generated by a different device that you have with you, such as your phone. When I connect to SSH I will get this prompt before a session is allowed:
-
1
I used to use RDP frequently also. For very similar reasons, I always changed the RDP port to a non-standard port.
— Mark Bowker
add a comment